The SolarisTM Zones facility in the Solaris Operating System provides an isolated environment in which to run applications on your system. Solaris Zones are a component of the Solaris Container environment.
Solaris Containers is Sun's operating system virtualization technique. A Solaris Container is the combination of system resource controls and the boundary separation provided by zones. Zones act as completely isolated virtual servers within a single operating system instance. By consolidating multiple sets of application services onto one system by placing each into isolated virtual server containers, system administrators can reduce cost and provide all the same protections of separate machines on a single machine.
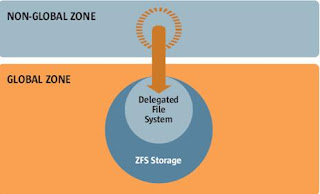
ZFS uses a pooled storage model in which storage capacity is held within an expandable pool called a zpool. Multiple file systems can exist within a zpool and they can share the capacity and IO resources of the pool. This new architectural approach, the storage version of virtual memory, permits easier administration of File systems and enables performance breakthroughs
Containers let you isolate ZFS file systems.
When To use Zones
Zones are ideal for environments that consolidate a number of applications on a single server. The cost and complexity of managing numerous machines make it advantageous to consolidate several applications on larger, more scalable servers.
The following figure shows a system with four zones. Each of the zones apps, users, and work is running a workload unrelated to the workloads of the other zones, in a sample consolidated environment. This example illustrates that different versions of the same application can be run without negative consequences in different zones, to match the consolidation requirements. Each zone can provide a customized set of services.
How Zones Work
A non-global zone can be thought of as a box. One or more applications can run in this box without interacting with the rest of the system. Solaris zones isolate software applications or services by using flexible, software-defined boundaries. Applications that are running in the same instance of the Solaris Operating System can then be managed independently of one other. Thus, different versions of the same application can be run in different zones, to match the requirements of your configuration.
A process assigned to a zone can manipulate, monitor, and directly communicate with other processes that are assigned to the same zone. The process cannot perform these functions with processes that are assigned to other zones in the system or with processes that are not assigned to a zone. Processes that are assigned to different zones are only able to communicate through network APIs. The global zone is the only zone from which a non-global zone can be configured, installed, managed, or uninstalled. Only the global zone is bootable from the system hardware. Administration of the system infrastructure, such as physical devices, routing in a shared-IP zone, or dynamic reconfiguration (DR), is only possible in the global zone. Appropriately privileged processes running in the global zone can access objects associated with other zones.
Unprivileged processes in the global zone might be able to perform operations not allowed to privileged processes in a non-global zone. For example, users in the global zone can view information about every process in the system. If this capability presents a problem for your site, you can restrict access to the global zone.
Each zone, including the global zone, is assigned a zone name. The global zone always has the name global. Each zone is also given a unique numeric identifier, which is assigned by the system when the zone is created.
How to configure a zone.
Note that the only required elements to create a native non-global zone are the zonename and zonepath properties. Other resources and properties are optional. Some optional resources also require choices between alternatives, such as the decision to use either the dedicated-cpu resource or the capped-cpu resource.
You must be the global administrator in the global zone to perform this procedure.
1. Become superuser, or assume the Primary Administrator role
• Set up a zone configuration with the zone name you have chosen.
The name my-zone is used in this example procedure.
global# zonecfg -z my-zone
If this is the first time you have configured this zone, you will see the following system message:
my-zone: No such zone configured
Use 'create' to begin configuring a new zone.
• Create the new zone configuration.
This procedure uses the Sun default settings.
zonecfg:my-zone> create
• Set the zone path, /export/home/my-zone in this procedure.
zonecfg:my-zone> set zonepath=/export/home/my-zone
Do not place the zonepath on ZFS for this release.
• Set the autoboot value.
If set to true, the zone is automatically booted when the global zone is booted. Note that for the zones to autoboot, the zones service svc:/system/zones:default must also be enabled. The default value is false.
zonecfg:my-zone> set autoboot=true
• Set persistent boot arguments for a zone.
zonecfg:my-zone> set bootargs="-m verbose"
• Dedicate one CPU to this zone.
zonecfg:my-zone> add dedicated-cpu
a. Set the number of CPUs.
zonecfg:my-zone:dedicated-cpu> set ncpus=1-2
b. (Optional) Set the importance.
zonecfg:my-zone:dedicated-cpu> set importance=10
c. The default is 1.
d. End the specification.
zonecfg:my-zone:dedicated-cpu> end
• Revise the default set of privileges.
zonecfg:my-zone> set limitpriv="default,sys_time"
This line adds the ability to set the system clock to the default set of privileges.
• Set the scheduling class to FSS.
zonecfg:my-zone> set scheduling-class=FSS
• Add a memory cap.
zonecfg:my-zone> add capped-memory
a. Set the memory cap.
zonecfg:my-zone:capped-memory> set physical=50m
b. Set the swap memory cap.
zonecfg:my-zone:capped-memory> set swap=100m
c. Set the locked memory cap.
zonecfg:my-zone:capped-memory> set locked=30m
d. End the memory cap specification.
zonecfg:my-zone:capped-memory> end
• Add a file system.
zonecfg:my-zone> add fs
a. Set the mount point for the file system, /usr/local in this procedure.
zonecfg:my-zone:fs> set dir=/usr/local
b. Specify that /opt/local in the global zone is to be mounted as /usr/local in the zone being configured.
zonecfg:my-zone:fs> set special=/opt/local
c. In the non-global zone, the /usr/local file system will be readable and writable.
d. Specify the file system type, lofs in this procedure.
zonecfg:my-zone:fs> set type=lofs
e. The type indicates how the kernel interacts with the file system.
f. End the file system specification.
zonecfg:my-zone:fs> end
This step can be performed more than once to add more than one file system.
• Add a ZFS dataset named sales in the storage pool tank.
zonecfg:my-zone> add dataset
a. Specify the path to the ZFS dataset sales.
zonecfg:my-zone> set name=tank/sales
b. End the dataset specification.
zonecfg:my-zone> end
• (Sparse Root Zone Only) Add a shared file system that is loopback-mounted from the global zone.
Do not perform this step to create a whole root zone, which does not have any shared file systems. See the discussion for whole root zones in Disk Space Requirements.
zonecfg:my-zone> add inherit-pkg-dir
a. Specify that /opt/sfw in the global zone is to be mounted in read-only mode in the zone being configured.
zonecfg:my-zone:inherit-pkg-dir> set dir=/opt/sfw
b. ________________________________________
c. Note –
d. The zone's packaging database is updated to reflect the packages. These resources cannot be modified or removed after the zone has been installed using zoneadm.
e. End the inherit-pkg-dir specification.
zonecfg:my-zone:inherit-pkg-dir> end
This step can be performed more than once to add more than one shared file system.
________________________________________
Note –
If you want to create a whole root zone but default shared file systems resources have been added by using inherit-pkg-dir, you must remove these default inherit-pkg-dir resources using zonecfg before you install the zone:
• zonecfg:my-zone> remove inherit-pkg-dir dir=/lib
• zonecfg:my-zone> remove inherit-pkg-dir dir=/platform
• zonecfg:my-zone> remove inherit-pkg-dir dir=/sbin
• zonecfg:my-zone> remove inherit-pkg-dir dir=/usr
________________________________________
• (Optional) If you are creating an exclusive-IP zone, set the ip-type.
zonecfg:my-zone> set ip-type=exclusive
________________________________________
Note –
Only the physical device type will be specified in the add net step.
________________________________________
• Add a network interface.
zonecfg:my-zone> add net
a. (shared-IP only) Set the IP address for the network interface, 192.168.0.1 in this procedure.
zonecfg:my-zone:net> set address=192.168.0.1
b. Set the physical device type for the network interface, the hme device in this procedure.
zonecfg:my-zone:net> set physical=hme0
c. End the specification.
zonecfg:my-zone:net> end
This step can be performed more than once to add more than one network interface.
• Add a device.
zonecfg:my-zone> add device
a. Set the device match, /dev/sound/* in this procedure.
zonecfg:my-zone:device> set match=/dev/sound/*
b. End the device specification.
zonecfg:my-zone:device> end
This step can be performed more than once to add more than one device.
• Add a zone-wide resource control by using the property name.
zonecfg:my-zone> set max-sem-ids=10485200
This step can be performed more than once to add more than one resource control.
• Add a comment by using the attr resource type.
zonecfg:my-zone> add attr
a. Set the name to comment.
zonecfg:my-zone:attr> set name=comment
b. Set the type to string.
zonecfg:my-zone:attr> set type=string
c. Set the value to a comment that describes the zone.
zonecfg:my-zone:attr> set value="This is my work zone."
d. End the attr resource type specification.
zonecfg:my-zone:attr> end
• Verify the zone configuration for the zone.
zonecfg:my-zone> verify
• Commit the zone configuration for the zone.
zonecfg:my-zone> commit
• Exit the zonecfg command.
zonecfg:my-zone> exit
Note that even if you did not explicitly type commit at the prompt, a commit is automatically attempted when you type exit or an EOF occurs.
Subscribe with a valid E-mail id so that you can get the latest updates posted in this site in your e-mails.



2 comments:
it's really very use full.......
how to cancel norton subscription
avast turn off auto renewal
Post a Comment